Ten reasons to use OPC UA
Guide:
OPC UA
The OPC Unified Architecture is a new technology created by the OPC Foundation that is safer, more reliable, and neutral (independent of the vendor) for manufacturing site-to-production planning or enterprise resource planning (ERP) systems. Raw data and preprocessed information. With OPC UA technology, all the information you need can reach every authorized application and every authorized person anytime, anywhere.
OPC UA is independent of the manufacturer, the application can communicate with him, the developer can develop it in different programming languages, and he can support him on different operating systems. OPC UA complements existing OPCs and adds important features such as platform independence, scalability, high availability, and Internet services.
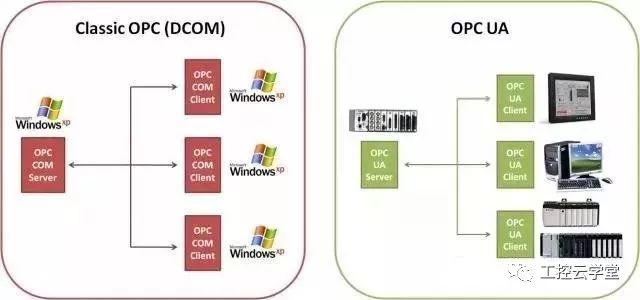
OPC UA is no longer based on the Distributed Component Object Model (DCOM), but is based on a Service Oriented Architecture (SOA). OPC UA can therefore connect more devices.
Today, OPC UA has become the bridge between enterprise-class computers and embedded automation components - independent of Microsoft, UNIX or other operating systems.
The following body part
1. Termination of the Component Object Model (COM) / Distributed Component Object Model (DCOM)
Data exchange between traditional OPC applications is based on Microsoft's Component Object Model (COM) technology. Because the Windows operating system has been widely used worldwide, and it also promotes the use of Windows computers in automation, COM technology has also created conditions for the widespread use of OPC technology. In early 2002, Microsoft released a new .NET framework and announced the discontinuation of COM technology. Although this does not mean that the future Windows operating system does not support COM, as a result of the cessation, the basic technology of the traditional OPC has not been developed, or will be eliminated sooner or later, so it is necessary to seek a new alternative.
2. Limitations of COM
In the 1990s, with the popularity of Windows computers, a set of features introduced by Microsoft COM/DCOM technology was highly appreciated by home computer users and industrial automation users. These features include copy and paste, drag and drop, linking and embedding. DCOM also provides a complete communications infrastructure with the necessary security mechanisms such as authorization, authentication and encryption. DCOM security mechanisms enable remote access to data and programs by computers. But DCOM security also challenges installation engineers, system integrators, and developer management projects, including OPC communications across PCs. Properly setting DCOM security features is a very difficult task and requires a lot of professional knowledge. As a result, installation engineers and system integrators routinely choose a fast process to take loose access authorizations on all networked OPC computers, causing most protections to be ineffective and allowing unauthorized remote access. This approach is contrary to the requirements of information technology (IT) security. In the long run, there may be danger of damage caused by careless or deliberately damaged people. DCOM security settings often require a special ability, and configuring OPC communication is very easy.
3. OPC communication through the firewall
In the automation industry, it has long been recognized that OPC communication needs to cross computer boundaries, which is another place where DCOM limits traditional OPC communication. DCOM requires multiple ports, such as authentication, data transfer, and a set of services to establish a connection. Therefore, many ports have to be opened in the firewall in order for DCOM communication to pass through him. Every port opened on the firewall is a security risk, providing a potential for hacker attacks. Tunneling in OPC UA is a widely accepted strategy that addresses the issue of DCOM limitations in traditional OPC products.

4. Use OPC on non-windows platforms
In industrial applications, the almost "ubiquitous" Microsoft platform, DCOM as a component of the operating system is an important factor that traditional OPC can be quickly accepted. But at the same time, the OPC integration concept is not good when using other operating systems, because they do not support DCOM. This is the case, for example, in the IT industry, where Unix or Linux systems are often used.
The same is true for automation, and some application areas explicitly refuse to use the Windows operating system. The field of embedded devices is another area where windows are difficult (except for Windows CE or embedded XP). Here, complex applications are embedded directly into field devices, PLCs, operating panels and other devices. They run VxWorks, QNX, embedded Linux, RTOS or other embedded operating systems without DCOM. The integration concept of using OPC in these areas is doomed to failure, because OPC requires DCOM as the technical foundation, and this foundation is missing in the embedded system.
5. Cross-platform OPC communication through Web services
With the release of the 2003 OPC XML-DA specification, the OPC Foundation demonstrated for the first time a way that is independent of the Windows platform and a way to overcome DCOM limitations. Today, many OPC XML-DA products demonstrate OPC technology based on Web services. However, the data throughput of XML-DA communication is still not as good as DCOM, and the communication speed is 5 to 7 times slower. This speed is too slow for many automation requirements. The OPC communication function based on Web services is still useful because it realizes the ability to cross the operating system, but further improve the data transmission performance.
6. Unified data model
To date, traditional OPC technology has three different OPC servers – data access servers, alarm and event servers, and historical data access servers. If the user needs to obtain the current value of a temperature sensor, an event whose temperature exceeds the limit value and a historical average of a temperature, then he must send 3 requests to access 3 servers. It takes a lot of time for users to access process data, events, and historical data in different ways. Therefore, unifying these three object models can make such things very simple, not only for the suppliers of OPC products, but also for system integrators and users.
7. Support complex data structures
One of the main applications of OPC is the operation and monitoring of serial communication or fieldbus networking equipment. In order to configure the device, the OPC client needs to write the data type to reach the device through the OPC server, including the meaning of the data structure components. The OPC Foundation has created a method for describing complex data structures, namely complex data specifications. However, most traditional OPC products on the market today cannot use complex data specifications with few exceptions.
8. Ensure communication does not lose data
The earliest defined data access allows the client application cycle to obtain the current state of the process data. If there is a problem with the physical communication connection between the OPC client and the remote OPC server, the data communication will be damaged. When the communication is corrupted, the data transferred to the OPC client will change or even be lost. This data loss is not critical in some data access applications, such as trend logging, process monitoring, or process display. But it is very important in some applications. For example, OPC technology has become the foundation of these regions, such as the chemical or petrochemical industries, where local data must be recorded seamlessly. In order to achieve this goal, suppliers need to implement a special extension method. They use a connection-based monitoring system to ensure rapid detection of disconnected traffic, automatic reconnection if communication is disconnected, and data caching, redundancy, storage, and forwarding in the data access server. These extended methods are useful, but are not defined in the traditional OPC specification and will vary from vendor to vendor.
9. Increased protection for unauthorized data access
As Ethernet-based communications in the automation industry continue to grow, automation and office networks have become entangled. At the same time, the idea of ​​vertical integration has created new demands, and this type of integration has also brought new security risks. OPC also adds to the use of remote maintenance and remote control concepts. Once again, it is mentioned that unauthorized access to the perimeter must meet more stringent information security requirements. As cybercrime, espionage and sabotage grows, information technology security becomes more and more important – so there are security requirements for using OPC. Traditional OPC vendors do not develop proprietary precautions and therefore cannot meet these security requirements.
10. Support for new command calls
In many applications, not only is it easy to read and write values, but it is also important to execute commands such as starting or stopping a drive or downloading a file to a device. The OPC command specification defines the method of executing these commands, but this is only valid in OPC UA and cannot be used in traditional OPC.
Plug-In Connecting Terminals,Insulated Spade Terminals,Cable Connector Double Spade Terminals,Vinyl-Insulated Locking Spade Terminals
Taixing Longyi Terminals Co.,Ltd. , https://www.longyicopperlugs.com