Paul Dillien, High Tech Marketing, Dr. Tom Kean, Algotronix
Cloud storage and IT service outsourcing are very attractive to IT managers because it not only reduces costs, but also reduces support work. However, there is a big concern that doing so will send sensitive data out of the company's firewall and pose a security risk. This concern is completely understandable because information is the most valuable asset for many companies, whether it is accounting, customers, or manufacturing-related data.
Now, equipment manufacturers can improve performance and security by using Xilinx FPGA-based solutions. The Algotronix Integrated Security Subsystem, which meets the MACsec requirements of the new Ethernet standard, uses Xilinx FPGA-based high-performance, low-latency, energy-efficient IP cores.
FPGA-based solutions are much faster than software-based solutions. In addition, dedicated hardware can take over the system processor to handle other tasks such as deep packet inspection. Alternatively, designers can use lower-cost processors.
Encryption and authentication
A significant strategy for protecting information is to encrypt data as it travels through the network and moves around the data center. Once data is intercepted by an unauthorized party penetrating the network link, data encryption ensures that it cannot be read. In principle, data should also be certified to ensure its integrity. Message authentication is designed to detect whether the original encrypted data has been tampered with, including changes due to transmission errors, or maliciously vandalized by the attacker for profit.
At present, Ethernet transmission has become a mainstream communication method. This is a high-speed transmission method that is both efficient and scalable. With the popularization of Ethernet standards, the cost of Ethernet transmissions has been continuously reduced, and this advantage has made it even more compelling, thus ensuring that Ethernet continues to be the preferred L2 technology. However, just a few years ago, the Ethernet standard did not have any cryptographic requirements, and only encryption technologies such as IPsec running on top of the communication protocol stack could be used.
Now, according to the IEEE 802.1AE standard, a new version of the latest Ethernet standard has added a number of security measures. The technology was formally established a few years ago. It uses an integrated security system to encrypt and authenticate messages while detecting and responding to a series of cyber attacks. This standard is called the "Media Access Control Security" standard, often referred to simply as "MACsec". Algotronix has been working hard since a few years to introduce IP cores that provide hardware-accelerated encryption based on multiple data rate requirements. (Algotronix also offers an IPsec-oriented IP core, which is similar to the MACsec product interface and is a good choice for systems that need to support dual standards.)
Trust entity
MACsec refers to a series of trusted entities made up of nodes on the network. Each node can receive encrypted messages and plain text messages, and system policies are used to specify how to process each message. The kernel includes bypass options for clear messages without authentication or verification. Unlike protocols such as IPsec that run as end-to-end technologies on L3/L4, MACsec can decrypt and verify each packet as soon as packets enter or leave the Ethernet LAN.
MACsec is suitable for Ethernet topologies such as star or bus LAN, but also supports point-to-point systems.
The MACsec standard uses the SecY method, which means that each node or entity has a unique key linked to its Ethernet source address. To support multiple virtual SecYs, we designed a 1G version of the IP core. Therefore, a single Ethernet MAC can be equipped with multiple MACsec SecYs associated with it for applications such as multi-user LANs. MACsec is usually used in conjunction with IEEE 801.1X-2010 or Internet Key Exchange (IKE) to implement secure key distribution around the network.
The reason why the data center selects the L2 connection function to move data packets in the data center is to increase the speed and minimize the delay and reduce the overhead data in the data packet. In contrast, if you use secure L3 technologies such as IPsec to communicate, messages must be sent to the upper layer of the protocol for processing, which increases latency.
In addition, L2 solutions can also avoid the complex task of creating L3 security policies.
The data center can use MACsec to provide firewall background protection or use it on the direct link between data centers. System administrators can authorize devices to communicate in a secure manner. Devices can detect errors or misuses, such as denial of service attacks (DOS).
Meets programmable requirements
The market has become increasingly segmented due to different needs. Customizable FPGA solutions are ideally suited for MACsec. Initially, MACsec's design was applied as a technology to the metropolitan area network, and now it has found its place in the data center, which has increased the overall demand for FPGA-based solutions.
Algotronix's development of the MACsec core is a natural evolution because we have built a series of cryptographic engines called "AES-GCM." The operating speeds of these cores are 1G, 10G, and 40G, respectively. We achieve these rates by pipelining, increasing the clock rate, and gradually moving from Xilinx's Artix® devices to Kintex® devices to Virtex® FPGAs. We will use these technologies to drive the throughput on the Virtex UltraScaleTM devices to 100G.
We use the IP cores in the FPGA to achieve a variety of different performances that can support different rates from 1GbE to 10GbE (ie, the core's actual worst-case throughput). In addition, we also plan to introduce 40G and 100G versions. This is much faster than a software-based system. The core is usually connected directly to the hardware MAC (as shown in Figure 1) because the embedded memory software on the FPGA chip transfers data as fast as possible to meet its throughput requirements. If security is implemented in hardware and no unencrypted key is provided to the software, the system is less vulnerable to common software attacks such as Trojan horses and viruses. This makes it easier to analyze system vulnerabilities even if IT professionals must consider the entire software level of the system.
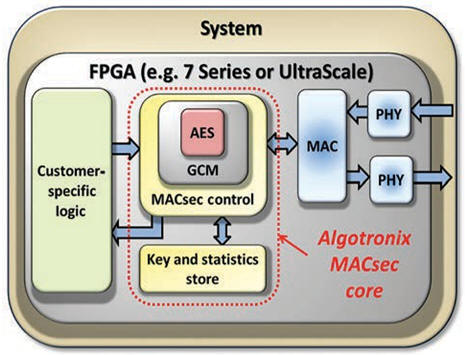
Figure 1 The entire MACsec IP core is located within the FPGA for maximum security.
Another important consideration is that FPGAs accelerate algorithms with systems that significantly reduce power consumption. Accelerated algorithms include encryption functions, etc., so as not to use software to achieve acceleration. FPGAs are significantly more energy efficient than software solutions.
An important attribute built into all Algotronix encryption cores is the ability to implement key blocks called "S-Boxes" in lookup tables (LUTs) in block RAM or FPGA fabrics. With this attribute, customers can use the existing resources to achieve the design by comprehensively balancing the two resource types. For example, if the design outside the MACsec core does not occupy a large amount of BRAM, then block RAM can be used to implement S-Boxes, otherwise LUTs are used.
MACSEC details
The MACsec system's design philosophy is that each data source uses a different encryption key. After receiving the message, the receiver will look in the list of on-chip CAMs to identify the correct key to decrypt the packet. Each packet is numbered to ensure that it can detect and reject duplicate or retransmitted packets. This method protects against "man in the middle" attacks.
MACsec also collects statistics on the number of rejected packets and the reason for the rejection. Providing statistical data to support attack detection is a higher level of security beyond basic encryption privacy, authentication, and retransmission prevention capabilities, allowing system managers to proactively respond to ongoing attacks.
The approach we take is to "package" the MACsec logic around the proven AES-GCM core. In this regard, designing an efficient and fast cryptographic kernel is only part of the design challenge. The MACsec standard covers a wide range of variables, including many variables.
For example, the standard initially specifies only 128-bit encryption keys. With a 128-bit key, the data is processed in the kernel after 10 conversions (called "rounds"). The standard has been revised to provide 256-bit encryption keys, and the entire digital encryption process has gone through 14 rounds. This is achieved by adding pipeline stages and increasing the memory bandwidth required for key storage.
MACsec has nothing to do with Ethernet traffic types, but is also transparent to higher layer protocols. With the introduction of these cores, MACsec can be easily added to the system, further enhancing network protection. MACsec-equipped sites can still communicate with other sites that do not use MACsec extra security mechanisms.
Ethernet packets are provided to the MACsec core from the media access controller (MAC). You can use a 1G MACsec core, an on-chip transceiver, and a triple-mode Ethernet MAC (TEMAC) to build an efficient, small solution. Each packet contains the destination and address of the source code that initiated the transfer. The standard is stored in the MACsec system, but an important factor is that in a multiple reflection transmission, the "source code" will be the address of the final device that delivers the data packet. Therefore, unlike IPsec, which can be viewed as an end-to-end scenario, MACsec works in a hop-by-hop manner. For each hop, MACsec requires all encrypted data on the input to be decrypted and then re-encrypted using the unique key assigned to the transmitting device. The decrypted plaintext can provide packet inspection capabilities at each level, as shown in Figure 2, and can also be used by the traffic manager to manage data flows.
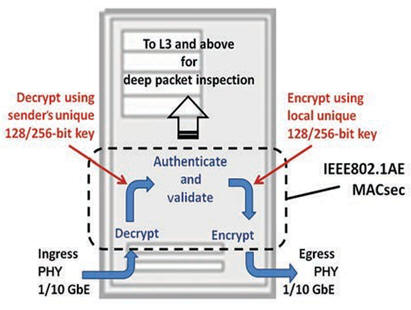
Figure 2 Messages are decrypted on the ingress port and encrypted on the egress port.
In the MACsec standard, the header shown in FIG. 3 contains an additional field "SecTAG", which defines the EtherType and indicates whether the packet is encrypted. When data is appended to the end of the message in the ICV field, it means that it has been authenticated.
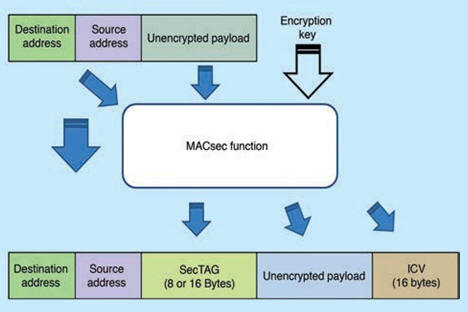
The MACsec frame structure in Figure 3 includes the MAC Security Tag (SecTAG) field, which defines the EtherType and indicates whether the packet is encrypted.
The ICV cooperates with the encryption key to authenticate the frame including the header and the MACsec tag, thereby ensuring that the source and destination addresses of the frame are not tampered with. We implement this logic in the FPGA fabric to ensure it has fast, predictable timing to minimize latency.
The MACsec core includes a lookup table connected to each source address. The key contained in this table must be able to successfully decrypt the message. We have carefully designed this function so that it can be efficiently implemented in the LUT and the device's block RAM. We take full advantage of the flexibility of the FPGA solution, and use the implementation options (such as 128-bit or 256-bit key, but also modify the number of virtual SecY supported by the kernel) to design the kernel.
Another important feature of the new standard is that MACsec collects packet-level statistics. System administrators can learn about information (such as how many packets were rejected due to delay, or failed the integrity check because of an invalid decryption key or use of the wrong key), and the statistics and the number of correctly transmitted packets Compare.
The MACsec standard provides thin options for point-to-point applications. This eliminates the need to use CAM to determine keys from explicit secure channel identifiers and single-to-multipoint operations in the packet. Our kernel can also support multiple virtual SecYs associated with a single Ethernet so that different keys can be used to encrypt data transmitted from the MAC to different destinations. The MACsec standard defines this configuration as a multi-user LAN because it is as if these destinations are on different Ethernet LANs. This feature allows the system to partition the receiving device by using different keys to encrypt the output.
The data center may use multiple SecYs to create virtual partitions so that customer A's data can be separated from customer B's data by a unique encryption key.
Internal data center communications can be organized as needed to separate selected racks to provide virtual isolation. This feature protects data integrity and addresses isolation issues in data centers and cloud applications. Whether it is an accidental error connection or malicious behavior (see Figure 4), the MACsec system can detect unauthenticated packets, and the system administrator can quarantine or delete them by setting policies.

Figure 4 MACsec will reject packets arriving on the wrong connection, whether due to an unexpected situation or malicious behavior.
All data encryption and decryption are done at the port level. In addition to the additional MACsec header and less additional latency, opening port-level encryption does not increase overhead and does not have other performance implications.
By adopting the encrypted Ethernet Lecel 2 solution that meets the IEEE 802.1AE requirements, equipment vendors can now use these cores to promote their system features. Cloud-based users may not trust each other with other users, but they are now able to benefit from the confidentiality of data provided by MACsec, and data source authentication capabilities can further protect their data.
Device manufacturers can choose the available IP cores to meet the needs of 1Gb and 10Gb Ethernet throughput.
This architectural design can easily achieve 10 Gbps speeds with Kintex or Virtex FPGA devices. In the worst case scenario, the design only needs to change the key of each packet to support Jumbo Frames and Minimal Packets. The core meets the full specification requirements and each MACsec core can support a variety of commonly used FPGA product families.
Supporting source code
Algotronix took unusual measures to provide HDL source code for all licensed cores. The main motivation for doing this is to support customer inspections to ensure that the code is free of viruses or Trojan horse code and that it will not be forced into an unauthorized state or operation. With source code, you can reduce the cost and complexity of customer security audits. In addition, source code can speed up the design process because engineers can easily try out different configuration parameters and key lengths such as encryption, decryption, or encryption/decryption, and understand the signal states in their respective emulation cores.
You can configure the core to increase throughput by implementing a wider data path, or minimize FPGA package size by choosing a narrower data width. Having source code has many other advantages, including easier understanding of the kernel's work; it also makes documentation and archiving faster and easier.
In addition, an extensive verification test platform is provided to help customers confirm the correct operation in tools such as ModelSim. The test platform includes MACsec's behavioral model and a self-test version of the MACsec IP core that can examine the output of synthesizable hardware against the behavioral model. This self-inspection design can be instantiated in user simulations to facilitate the testing of kernel performance in the actual user's design environment and provide useful diagnostic information in case of error-driven conditions.
The kernel offers many options, so the exact amount of resources will depend on how you choose parameters such as data rate, key length, and selected SecY quantity and others. However, the 10G MACsec core listed in the IP section of the Xilinx website uses 6,638 slices, 20,916 LUTs, and 53 BRAM blocks. For license options, contact Algotronix.
The combination of Xilinx low-power FPGAs and Algotronix MACsec cores provides device manufacturers with high-performance, low-latency solutions for product differentiation. Security features allow the data center to secure its clients, while also helping security administrators detect and combat malicious behavior.
DADNCELL 1.5V AAA alkaline batteries are more suitable for
long-lasting continuous discharge and high-performance power consumption
equipment because of their unique internal component structure, coupled with
better battery materials, improved power capacity and electrical performance,
and the same model of DADNCELL 1.5V AAA alkaline cell capacity and discharge time, Alkaline
battery capacity and discharge time are 4-7 times that of ordinary batteries,
and the gap in power discharge performance at high and low temperature is even
wider.
At present, all types of cells developed by DADNCELL Labs do not involve any
heavy metals in production, are green and can be disposed of with domestic
waste.
DADNCELL 1.5V AAA battery advocates a more comfortable and smooth
power supply experience for household appliances. Alkaline zinc-manganese dry
battery series is suitable for various common household electronic equipment
instruments such as smart door locks, infrared thermometers, cameras, flash
lights, razors, electric toys, instruments, high-power remote controls,
Bluetooth wireless mouse keyboards, etc.
1.5V Aaa Alkaline Battery,1.5V Alkaline Battery For Cameras,Lr03 Zinc-Manganese Cells For Electronic Product,Electronic Equipment Am-4 1.5V Battery
Shandong Huachuang Times Optoelectronics Technology Co., Ltd. , https://www.dadncell.com